Intro
I have a second laptop principally used by another person though I set up an initial account on it with admin privileges. I’ve written it up before with a glowing review. it’s the HP Pavilion Aero – a line of laptops no longer produced it seems. When I initially got it it had a problem using its built-in WiFi. I wrote that up in a post I see the search engines have mostly passed on, too bad, Windows 11 wipes out Mediatek driver.
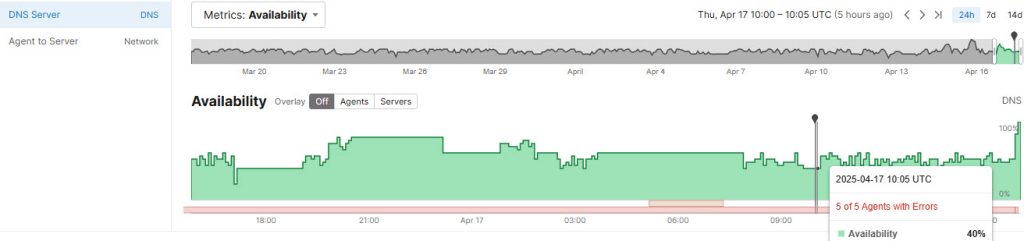
Well, wouldn’t you know that last Friday, after the 2025-05 Cumulative Update for Windows 11 24H2 was applied, bang, similar thing happened. WiFi just wouldn’t connect for the primary user. The tray icon showed the globe. You can see various SSIDs, but when you try to connect it connects for a half-second then says Can’t connect to this network.
Additional paragraph with stuff.
The details
This post qualified as an IT Detective series article only because I did various things, it began to work, and I think I have established the correlation with what I did and the fix. So I have been planting little hints in the Intro to this article as is the detective series requires.
So, any ideas so far?
Here’s the thing. Honestly, I went back to my original article because the HP advice on this issue looked out of date and time-consuming and I just didn’t want to do it. Stuff like, re-install the driver. Windows was already uptodate so no problems there. And I did try to run the HP PC hardware diagnostics tool, but honestly, it produces an error in trying to run and I didn’t want to go down that rabbit hole tryig to resolve that, or trying to get into the BIOS settings.
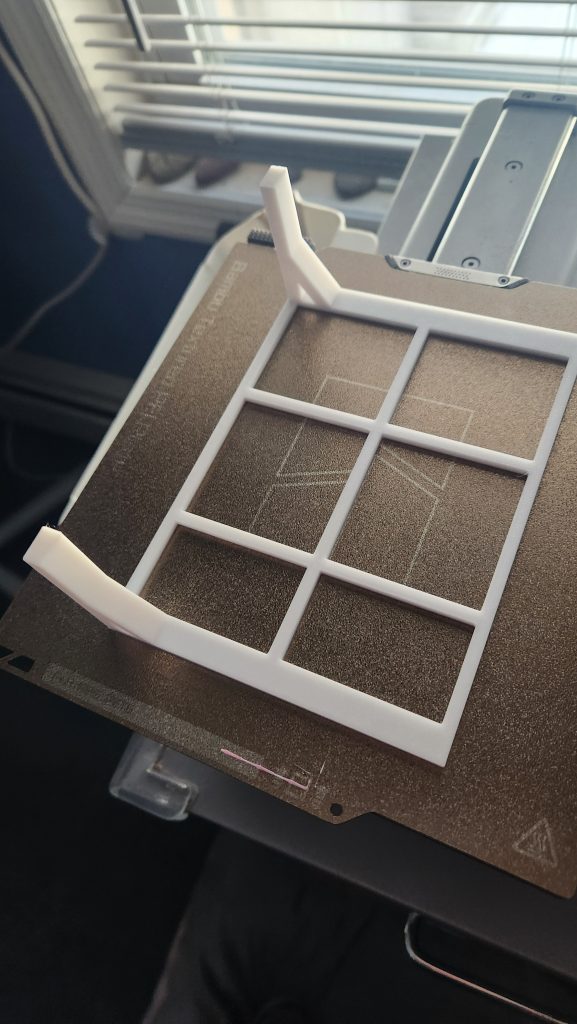
I did dig up an old Edimax tiny WiFi dongle. The thing probably sticks out 5 mm, I had it since 2014 for my Raspberry Pi days. That was when, in the RPi 2 line, they didn’t even come with built-in WiFi! so, yeah, the proximate problem was solved. The Edimax was immediately recognized, no driver install needed. Now there are two WiFi things. You pick WiFi 3. You have to retype any and all WiFi passwords previously used. It’s only wiFi 4, but adequate. Meanwhile I order the newer version which support WiFi 5.
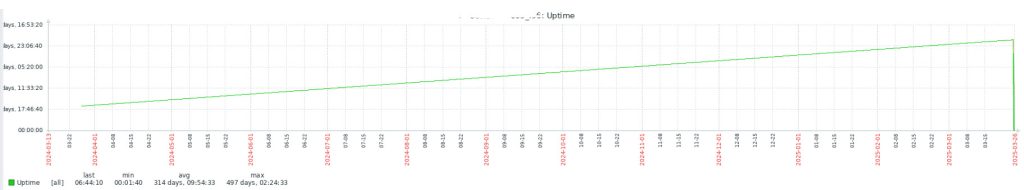
But in the back of my head I knew I had to try to do a real fix. I decided to switch accounts on the laptop to my account, which to remind you is set up as the administrator. I glanced at the wireless status in the vain hopes it would magically appear to be working. But I saw the globe. Then it said set up completing, it will take a few minutes. I let it through its paces.
At some point I noticed that the built-in WiFi was working!
I logged out and switched to the normally-used account. Still working!
What you see when you plug in an external USB WiFi adapter
What changes in Windows 11 when you have both the internal and external WiFi is not here. The Manage WiFi Connections remains the same:
But once you have clicked on that right-pointing arrow, you have an additional drop-down which shows up just above the list of all available SSIDs. It will display for instance WiFi by default, but since it’s a drop-down, the new one, say WiFi 3 (I have also seen it called WiFi 2) can be selected.
And that is how you work with multiple WiFi adpaters!
Conclusion
Although the Windows 2025-05 update initially wiped out the built-in WiFi on our HP Pavilion laptop, it cured itself once we logged in with the initial administrator account and allowed that account to complete its setup. We did not need to bother with going into BIOS and enabling whatever as we did when we initially had a similar problem years ago.
We found that the EDIMAX nano WiFi USB adapter works great to tide you over and deliver WiFi while you are fixing the built-in WiFi.
Case: closed
As I write this I have also tested the more uptodate EDIMAX WiFi adapter, the AC600. It also has a nano size, supports plug-and-play, dual band 2.4G/5G and works in both of my HP Pavilion home laptops.
References and related
The original post: Windows 11 wipes out Mediatek driver.
My glowing review of this HP Pavilion Aero laptop