Intro
It’s convenient to name drop different types of cyber attacks at a party. I often struggle to name more than a few. I will try to maintain a running list of them.
But I find you cannot speak about cybersecurity unless you also have a basic understanding of information technology so I am including some of those terms as well.
As I write this I am painfully aware that you could simply ask ChatGPT to generate a list of all relevant terms in cybersecurity along with their definitions – at least I think you could – and come up with a much better and more complete list. But I refuse to go that route. These are terms I have personally come across so they have special significance for me personally. In other words, this list has been organically grown. For instance I plowed through a report by a major vendor specializing in reviewing other vendor’s offerings and it’s just incredible just how dense with jargon and acronyms each paragragh is: a mother lode of state-of-the-art tech jargon.
Terms from history
I’ve thrown in some terms from my personal history having spent decades in the field, terms I’m pretty sure you won’t find in anyone else’s standard dictionary, like, let’s say xmosaic.
AiTM (Adversary in the Middle)
Bad Likert Judge
A technique for jailbreaking LLMs.
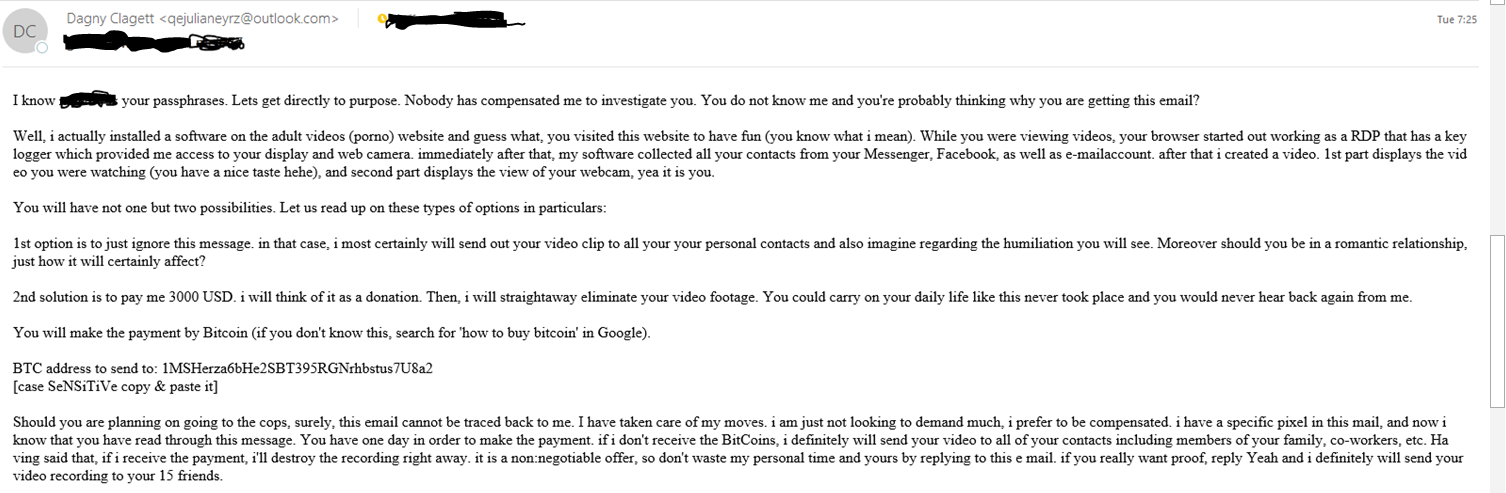
Baitortion
I guess an attack which has a bait such as a plum job offer combined with some kind of extortion? The usage was not 100% clear.
bootkit
BYOVD (Bring Your Own Vulnerable Driver)
Clickfix infection chain
Upon visiting compromised websites, victims are redirected to domains hosting fake popup windows that instruct them to paste a script into a PowerShell terminal to fix an issue.
Collision attack
I.e., against the MD5 hash algorithm as done in the Blast RADIUS exploit.
Credential Harvesting
Credential Stuffing Attack
I.e., password re-use. Takes advantage of users re-using passwords for different applications. Nearly three of four consumers re-use password this way. Source: F5. Date: 3/2024
CSRF (Cross-Site Request Forgery)
Unauthorized commands are submitted from a user that the web application trusts. Also XSRF.
Data Wiper
Authentication Bypass
See for instance CVE-2024-0012
Email bombing
A threat actor might flood a victom with spam then offer “assistance” to fix it.
Evasion
Malicious software built to avoid detection by standard security tools.
Password spraying
A type of attack in which the threat actor tries the same password with multiple accounts, until one combination works.
Port Scan
Self-describing.
ProxyLogon
Affected MS Exchange and exploited by Silk Typhoon.
XSRF (Cross-site Request Forgery)
See CSRF.
Host Sweep
Supply Chain attack
Social Engineering
Hacking
Hacktivist
I suppose that would be an activitst who uses hacking to further their agenda.
Hex Staging
No idea. Insufficient context in the place where I read the term.
Jailbreaking
A form of privilege escalation. Removing limitations of an OS like Android or iOS.
Living off the land
Network reconnaissance
Data Breach
Keylogger
Darknet
Captcha
Click farms
DLL hijacking
Jackpotting
This is one of my favorite terms. Imagine crooks implanted malware into an ATM and were able to convince it to dispense all its available cash to them on the spot! something like this actually happened. Scary.
Overlay Attack
Example: When you open a banking app on your phone, malware loads an HTML phishing page that’s designed to look just like that particular app and the malware’s page is overlaid on top.
Payment fraud attack
In a recent example, the victim experienced “multiple fraudulently induced outbound wire transfers to accounts controlled by unknown third parties.”
PlugX
A type of malware.
Skimmer
XSS (Cross site Scripting)
bot
Anti-bot, bot defense
Mitigation
Selenium (Se) or headless browser
Obfuscation
PII, Personally Identifiable Information
api service
Reverse proxy
Inline
endpoint, e.g., login, checkout
scraping
Layer 7
DDOS
Carpet bombing DDOS attack
Many sources hitting many targets within the same subnet. See:
SYN flood
DOS
Visibility
Automation
Token
Post
JavaScript
Replay
Browser Fingerprint
OS
Browser
GDPR
AICPA Trust Services
Grandparent scam
A social engineering attack where scammers target grandparents by pretending to be a grandchild in a bind.
GUI
(JavaScript) Injection
Command Injection
Hotfix
SDK
Method
TLS
Clear text
X-Forwarded-For
Client/server
Threat Intelligence
Prompt Injection
A malicious prompt given to an AI model.
XPIA (Cross-Prompt Injection Attack)
Indirect Prompt Injection
LLM scope violation
New term as of June 2025.
Carding attack
Source code
CEO Fraud
Phishing
TOCTOU (Time-of-Check Time-of-Use)
Vulnerability in VMWare ESX.
Vishing
(Voice Phishing) A form of cyber-attack where scammers use phone calls to trick individuals into revealing sensitive information or performing certain actions.
Business email compromise (BEC)
VEC (Vendor Email Compromise)
Deepfake
Threat Intelligence
Social engineering
Cybercriminal
SIM box
Command and control (C2)
Typo squatting
Voice squatting
A technique similar to typo squatting, where Alexa and Google Home devices can be tricked into opening attacker-owned apps instead of legitimate ones.
North-South
East-West
Exfiltrate
Malware
Infostealer
Obfuscation
Antivirus
Payload
Sandbox
Control flow obfuscation
Buffer overflow
Use after free
Indicators of Compromise
AMSI (Windows Antimalware Scan Interface)
Polymorphic behavior
WebDAV
Protocol handler
Firewall
Zero Trust
Zero Trust is a security model that assumes that all users, devices, and applications are inherently untrustworthy and must be verified before being granted access to any resources or data.
Zero Trust Network Access (ZTNA)
ZTA (Zero Trust Architecture)
Zero Trust Edge (ZTE)
Secure Web Gateway (SWG)
Cloud Access Security Broker (CASB)
Remote Browser Isolation (RBI)
Content Disarm and Reconstruction (CDR)
Firewall as a service
Egress address
Data residency
Data Loss Prevention (DLP)
Magic Quadrant
Managed Service Provider (MSP)
0-day or Zero day
User Experience (UX)
Watermark
DevOps
Multitenant
MSSP
Remote Access Trojan (RAT)
SOGU
2024. A remote access trojan.
Object Linking and Embedding
(Powershell) dropper
Backdoor
Data Bouncing
A technique for data exfiltration that uses external, trusted web hosts to carry out DNS resolution for you
Infostealer
Shoulder surfing
Ransomware
Pig butchering
This is particularly disturbing to me because there is a human element, a foreign component, crypto currency, probably a type of slave trade, etc. See the Bloomberg Businessweek story about this.
Forensic analysis
Sitting Ducks
An entirely preventable DNS hijack exploit. See https://blogs.infoblox.com/threat-intelligence/who-knew-domain-hijacking-is-so-easy/
SSRF (Server-Side Request Forgery)
Server site attack that leads to sensitive information disclosure from the back-end server of the application
Attack vector
Economic espionage
Gap analysis
AAL (Authentication Assurance Level)
IAL (Identity Assurance Level)
CSPM (Cloud Security Posture Management)
Trust level
Network perimeter
DMZ (Demilitarized zone)
Identity Farming
Sites set up to encourage unsuspecting victims to voluntarily hand over their identity documents and facial images in return for financial compensation.
Defense in depth
Lateral movement
Magecart
Malicious code is injected into a website to steal sensitive information, such as credit card details, from users filling out forms.
Access policy
Micro segmentation
Least privilege
Privilege Escalation (PE)
Breach
Intrusion
Insider threat
Cache poisoning
I know it as DNS cache poisoning. If an attacker manages to fill the DNS resolver’s cache with records that have been altered or “poisoned.”
Teardrop attack
A teardrop attack exploits how systems reassemble fragmented data packets during transmission by sending overlapping fragments that the target system cannot properly reconstruct, leading to a denial of service.
Verify explicitly
Network-based attack
Adaptive response
Telemetry
Analytics
Consuming entity
Behavior analysis
Authentication
Authorization
Real-time
Lifecycle management
Flat network
Inherent trust
Cloud native
Integrity
Confidentiality
Data encryption
EDR (Endpoint Detection and Response)
BSOD (Blue Screen of Death)
Everyone’s favorite Windows error!
BSI (Bundesamt für Sicherheit in der Informationstechnik)
German Federal Office for Information Security (Bundesamt für Sicherheit in der Informationstechnik)
Reverse shell
A text-based interfaces that allow for remote server control.
Crypto Miner
RCE (Remote Code Execution)
Threat Actor
APT (Advanced Persistent Threat)
Compromise
Vulnerability
Bug
Worm
Remote Access VPN (RAVPN)
XDR (Extended Detection and Response)
SIEM (Security Information and Event Management)
User Entity Behavior Analytics (UEBA)
Path traversal vulnerability
An attacker can leverage path traversal sequences like “../” within a request to a vulnerable endpoint which ultimately allows access to sensitive files like /etc/shadow.
Tombstoning
Post-exploit persistence technique
Volumetric DDoS
MFA bomb
Bombard a user with notifications until they finally accept one.
Use-after-free (UAF)
A use-after-free vulnerability occurs when programmers do not manage dynamic memory allocation and deallocation properly in their programs.
Cold boot attack
A cold boot attack focuses on RAM and the fact that it is readable for a short while after a power cycle.
Random Prefix Attack
A type of DNS attack. https://developers.cloudflare.com/dns/dns-firewall/random-prefix-attacks/
Famous named attacks
Agent Tesla
Cloudbleed
Heartbleed
log4j
Morris Worm
Explanations of exploits
Famous attackers
APT29 (Cozy Bear)
A Russia-nexus threat actor often in the news
Dark Storm
Formed in 2023 and known for its sophisticated cyber warfare attacks and successful hacks of high-security systems. Has a pro-Palestinian bent.
Scattered Spider
A financially motivated threat group, responsible for the 2025 Marks and Spencer breech.
Silk Typhoon
A Chinese-based group focused on espionage, now targeting common IT solutions to gain initial access, and then compromise these companies’ downstream customer environments.
Volt Typhoon
2024. A China-nexus threat actor
Cybersecurity Terminology
What makes a term a cybersecurity term versus an It term? I had to think about it a bit. There is a lot of overlap for sure. Today to be in IT is to be mindful of security every working moment of your day. So I ended up with just a few terms which I threw into this bucket of cybersecurity terminology. It was my judgment call.
360
360 Security Group is a respected vendor in the threat intelligence arena.
ABP (Advanced Bot Protection)
Imperva uses this term.
Aisuru
A 2025 botnet which unleashed 6 Terabits/s in a test DDOS.
Attack Surface
A loose way of talking about the variety of infrastructrure owned by an entity which is exposed to hacking.
ASM (Attack surface Management)
A testing and tracking tool a cyber security center might use.
Blast Radius
One of those annoying terms borrowed from the military that only marketing people like to throw around. It means what you think it might mean.
Blue Team – see Red Team
BSI (The German Federal Office for Information Security)
Cisco Talos
A cybersecurity technology and information security company that conducts threat research, vulnerability disclosure, and incident response for Cisco and its customers
CNI (Critical National Infrastructure)
CNNVD (China National Vulnerability Database of Information Security)
CNVD (China National Vulnerability Database)
China’s EUVD.
CTI (Cyber Threat Intelligence)
Checkpoint likes this term.
Cryptomining
CSAM
The process of identifying, categorizing, tracking, and managing information technology (IT) assets to ensure their integrity, confidentiality, and availability
CSP (Content Security Policy)
DDosia
A cross-platform program that conducts DDoS attacks with a pro-Russia bent against websites in Europe and other regions
DLP (Data Loss Prevention)
DLS (Data Leak Sites)
Sites where you can see who has had their data stolen.
Dwell Time
Time spent by a hacker in your network.
EUVD (European Vulnerability Database)
The EU answer to Mitre’s CVE. Serves as a centralized repository for cybersecurity vulnerabilities affecting ICT products and services across the EU and aims to provide a trusted resource for both public and private sectors.
Feroxbuster
Kali Linux tool designed to perform Forced Browsing. Forced browsing is an attack where the aim is to enumerate and access resources that are not referenced by the web application.
Hacktivism
Hacking done by activitsts.
HMI (Human Machnie Interface)
Comes up in the context of water systems.
Initial Access Broker
The agent who got access to a network and may hand it off to others.
IoC (Indicators of Compromise)
IR (Incident Response)
Malspam
Spam containing malware, I guess.
MITRE ATT&CK
NASL (Nessus Attach Scripting Language)
Nessus
An open source vulnerability scanner.
nmap
Command-line tool for basic port scanning.
Offensive Security
See red team.
OpenVAS (Open source Vulnerability Assessment Scanner)
The free scanner component of Greenborne Vulnerability Management.
Passkey
Modern authentication method designed to replace traditional passwords with a more secure and user-friendly alternative which is usually biometric-based.
Patch Tuesday
Microsoft releases patches for all their bugs on the first or second Tuesday of each month.
Pen Test (Penetration Test)
Red Team
In a red team/blue team exercise, the red team is made up of offensive security experts who try to attack an organization’s cybersecurity defenses.
Red Wolf
Company which offers A DDOS testing service.
Shodan
A search engine that allows users to find various types of devices connected to the internet, such as webcams, routers, and servers, plus what software versions are running.
TI (Threat Intelligence)
TOR (The Onion Router)
A series of network nodes which provide anonymity to its users. Mainly used for nefarious pruposes.
TTP (Tactics, Techniques and Procedures)
Virustotal
Portal used to check if a web site has vulnerabilities checking multiple sources.
WAF (Web Application Firewall)
Whitehat
The good guys.
IT terminology
I’ve chosen the terms I personally come across. I find most IT concepts not particularly difficult to understand, but they are usually coded in a firehose of shorthand references. So a reference is helpful. Thus I’ve also decided to include some terms specific to some of the more popular vendors – because you hear others talking about them using their terminology and shorthand references, and you want to know what they are saying. Some of the definitions are meant to be humorous, like Johnson’s dictionary.
2FA (2 Factor Authentication)
3G (3rd Generation)
Refers to the third generation of telecom technologies.
3PL (3rd Party Logistics)
802.1x
A (Address record)
Base DNS record type which turns a domain name into an IP address
AAAA
A DNS address record which resolves to an ipv6 address.
ACL (Access Control List)
AD (Active Directory)
ADO (Azure DevOps)
AFK (Away From Keyboard)
Agentic AI
Autonomous agents power by AI. Term becoming popular in 2025.
AGI (Artificial General Intelligence)
AGI is the theory and development of computer systems that can act rationally.
AIOps
Applying AI to IT operations.
AIP (Azure Information Protection)
This is the old name as of March 2025. See MPIP for the new name.
AIX
A Unix variant supported by IBM. It had really strange conventions.
ALPN (Application Layer Protocol Negotiation)
A TLS extension used to establish HTTP/2 connections without additional round trips.
AMI (Amazon Machine Image)
AMS (Access Management Systems)
Physical building access through authentication methods like passwords, biometrics, and multi-factor authentication.
Anaconda
A python development platform.
ANN (Artificial Neural Network)
Ansible
I would call it an open source orchestrator.
anti-aliasing
When you smooth out color in neighboring pixels.
anycast
Anydesk
A popular remote management software.
AP (Access Point)
apache
A formerly popular open source web server which became bloated with features.
APM (Application Performance Management)
ARD (Apple Remote Desktop)
ARIN (American Registry for Internet Numbers)
They dole out blocks of IPv4 and IPv6 public address space.
ARM
A processor architecture from ARM Corporation, as opposed to, e.g., x86. Raspberry Pis use ARM. I think Androids do as well.
ARP (Address Resolution Protocol)
ASCII
An early attempt at representing alpha-numeric characters in binary. Was very english-focussed.
ASN (Autonomous System Number)
Each AS is assigned an autonomous system number, for use in Border Gateway Protocol routing
ASN.1 (Abstract Syntax Notation One)
A standard interface description language (IDL) for defining data structures that can be serialized and deserialized in a cross-platform way.
ASPA (Autonomous System Provider Authorization)
An add-on to RPKI that allows an ASN to create a record that lists which ASNs can be providers for that ASN. The concepts are “customer” (an ASN) and “providers” (a list of ASNs). This is used to do hop by hop checking of AS paths.
ASR (Aggregation Services Router)
A high-end Interent router offered by Cisco for business customers.
Assembly
The raw instructions for a microprocessor to follow which results from compiling a program.
asuid (Application Service Unique Identifier, according to chatgpt)
Token sometimes found at the beginning of a dns FQDN.
AT (Authenticated Transfer [Protocol])
A protocol supporting social networking. Used by Bluesky.
At scale
A scaled-up deployment.
AutoIt
Scripting language designed for automating the Windows GUI (Graphical User Interface) and general scripting tasks. It allows users to create scripts that can simulate keystrokes, mouse movements, and manipulate windows and processes.
AV (anti-virus)
AWS (Amazon Web Services)
AZ (Azure)
Azure AD
Azure Local
Often referred to in the context of Azure Stack, is a set of products and services from Microsoft that allows organizations to run Azure services in their own data centers or on edge devices
B2B (Business-to-Business)
As opposed to B2C.
B2C (Business-to-Consumer)
Beacon
System which broadcasts keep alive data regularly, I think.
BeQ (not sure about this one yet)
BGP (Border Gateway Protocol)
BIND (Berkeley Internet Name Daemon)
An open source implementation of DNS, found on many flavors of linux.
BIOS (Basic Input/Output System)
BITNET
An early (pre-Internet) network for High Energy Physics which connected some universities in the US with some in Europe. I used to use it.
blob (Binary Large OBject)
Binary file
BOM (Bill of Material)
Boot start
A flag for a driver in Windows that tells it to always start on boot.
bootp
A predecessor protocol to DHCP.
broadcast
Browser
BYOD (Bring Your Own Device)
I.e., when employees are permitted to use their personal smartphone to conduct company business.
BYOL (Bring Your Own License)
F5 permits this approach to licensing one of their cloud appliances.
CA (Certificate Authority)
CAA (Certificate Authority Authorization)
DNS record that allows domain owners to specify which certificate authorities (CAs) are permitted to issue SSL/TLS certificates for a domain.
A type of DNS record.
CAB (Change Advisory Board)
May not be a universal term.
Callback
A routine designed to be called when someone else’s code is executing. At least that’s how I understand it.
CAPWAP (Control and Provisioning of Wireless Access Points)
A Cisco protocol where the WLCs control the APs.
CCNA (Cisco Certified Network Associate)
An entry-level IT certification covering Cisco products.
CDL (Cortex Data Lake)
Another Palo Alto Networks term.
CDR (Call Detail Record)
Metadata for a phone call.
CDN (Content Distribution Network)
CDP (Cisco Discovery Protocol)
This protocol allows devices connected to switch ports to learn what switch and which switch port they are connected to. It is a layer 2 protocol.
CDR (Cloud Detection and Response)
CDSS (Cloud Delivered Security Services)
Only used in Palo Alto Networks land.
CE (Customer Edge or Customer Equipment)
CGN or CGNAT (Carrier Grade NAT)
The address space 100.64.0.0/10 is handled specially by ISPs for CGN. RFC 6598
CHAP
Chatbot
A computer program that simulates human conversation with and end user.
Checksum
An XOR operation on binary data which creates a short and unique signature. Different algorithms may be used.
Chrome
An OS from Google based on linux and somewhat more inflexible and less buggy than Windows.
Chromebook
A laptop which runs CHROME OS.
Chromium
I think this is the open source(?) foundation for some browsers such as Edge.
CI (Configuration Item)
An ITIL term referring to the object upon which changes are made.
CI/CD (Continuous Integration/Continuous Delivery)
CIDR (Classless Internet Domain Routing)
The a.b.c.d/e notation, e.g., 192.168.1.0/24.
CIFS
A protocol related to Windows file shares.
CIPA (Children’s Internet Protection Act)
CISA (Cybersecurity and Infrastructure Security Agency)
CISC (Complex Instruction Set Architecture)
CISO (Chief Information Security Officer)
CISSP (Certified Information Systems Security Professional)
Cleartext
Format where no encryption has been applied.
CLI (Command Line Interface)
Client Server
Was all the rage 20 years ago.
CMDB (Configuration Management Database)
CMO (Current Mode of Operations)
CNAME (Canonical NAME)
DNS record which associates a name with another name.
CNN (Congruential Neural Network)
CO (Central Office)
Old telecom lingo.
Codec (Compressor-Decompressor)
A technology or software that encodes and decodes digital data streams or signals
Computer Vision
A field of AI that leverages machine learning and neutral networks to enable machines to identify and understand visual information such as images and videos.
Copilot
Microsoft’s AI built into their productivity software. Sorry, no more Clippy.
Courrier
A well-known fixed-width font.
CPE (Customer Premise Equipment)
CPU (Central Processing Unit)
CRL (Certificate Revocation List)
A primitive predecessor to OCSP.
CRM (Customer Resource Management)
Software delivered by, e.g., Salesforce.
CRUD (Create, Read, Update, and Delete)
Four basic operations used in managing data in databases and applications.
CSAM (Customer Success Account Manager)
CSPM (Cloud Security Posture Management)
CSR (Certificate Signing Request)
CSSA (Cyber Security Sharing and Analytics alliance)
CSV (Comma-Separated Values)
A simplified exchange format for spreadsheet data.
CUDA (Compute Unified Device Architecture)
A programming language (by Nvidia?) that lets developers write applications for GPUs.
CUPS (Common Unix Printing Systems)
curl
A simple browser for the command line.
Cursor
The underline thingy which shows where your typed text will be entered into a document or form.
CVE
CVEs, or Common Vulnerabilities and Exposures, are a maintained list of vulnerabilities and exploits in computer systems. These exploits can affect anything, from phones to PCs to servers or software. Once a vulnerability is made public, it’s given a name in the format CVE–. There are also scoring systems for CVEs, like the CVSS (Common Vulnerability Scoring System), which assigns a score based on a series of categories, such as how easy the vulnerability is to exploit, whether any prior access or authentication is required, as well as the impact the exploit could have.
CVSS (Common Vulnerability Scoring System)
Part of CVE lingo. A CVSS score of 10 as “achieved” by SAP in CVE-2025-31324 is the worst of the worst.
d-marc (Demarcation panel)
Telecom concept: a board where the handoff from cables from the street meet cables frmo the data center.
DAS (Distributed Antenna System)
An extensive network of strategically placed antennas throughout a building to enhance cellular coverage where it’s needed.
DAST (Dynamic Application Security Testing)
Data at rest
Data in motion
Data Plane
A physical security appliance separates data traffic from its management traffic, which transits the managemenbt plane.
Data Remanence
The residual representation of data that remains even after attempting to erase or initialize RAM.
DB (DataBase)
DBA (DataBase Admin)
DCV (Domain Control Validation)
See OV.
DCVaaS (Domain Control Validation as a Service)
CSC likes this term which concerns how certificates get created.
DDI (DNS, DHCP and IP address management)
Debian Linux
A nice distro which I prefer. It is free and open source. Its packages are relatively uptodate.
Deduplication
A data optimization technique used to eliminate duplicate copies of data.
Deep Learning
A subset of machine learningthat focus on using deep neural networks with multiple layers to model complex patterns in data.
Deepfake
A manipulated video or other digital representation produced by sophisticated machine-learning techniquies that yield seemingly realistic, but fabricated images and sounds.
DGA (Domain Generation Algorithm)
Auto-generated domain names used by C2 networks.
DHCP (Dynamic Host Control Protocol)
Distributed Cloud
A Gartner term for a SaaS service which runs over multiple cloud environments.
DLL (Dynamic Link Library)
It’s a Windows thing.
DMA (Digital Millenium Act)
A law intended to bring copyright into the digital age.
DNAC (DNA Center)
Cisco term. Managing network devices, automating network operations, etc.
DNAT (Destination NAT)
DNS (Domain Name System)
DNSSEC (Domain Name System Security Extensions)
DOA (Dead on Arrival)
Usage: That equipment arrived DOA!
Docker
DoH (DNS over HTTPS)
Domain
Downselect
Reducing the number of vendors under consideration during the RFP process. Term maybe only used in companies where I have worked??
dp (data independent pixel)
Unit which assumes a screen resolution of 160 pixels per inch.
DR (Disaster Recovery)
DRDC (Disaster Recovery Data Center)
Perhaps only used at my company?
DRM (Digital Rights Management)
DTLS (Datagram Transport Layer Security)
A communications protocol providing security to datagram-based applications by allowing them to communicate in a way designed to prevent eavesdropping, tampering, or message forgery.
DVI (DeVice Independent file)
See LaTEX entry.
EAP
East-West
Data movement with a data center, I believe, as oppose to North-South.
EBITDA (Earnings Before Interest, Taxes, Depreciation and Amortization)
Hey, an IT person needs to know some business terminology!
ECC (Elliptic Curve Cryptography)
Encryption type stronger than RSA
EDT
The first editor in the VAX/VMS world. It got renamed to TPU.
Eduroam
Enhanced Factory Reset (EFR)
Entra
From Microsoft. The new name for Azure AD
EntraID
Another way to refer to Entra from Microsoft.
ERM (Enterprise Risk Management)
ERP (Enterprise Resource Planning)
Expensive, monolithic software delivered by the likes of SAP. Typically used by large enterprises.
ERRP (Expired Registration Recovery Policy)
It’s an ICANN-specific acronym.
ETR (Estimated Time to Restore)
EU AI Act
EULA (End User License Agreement)
Exact Data Matching (EDM)
FAQ (Frequently Asked Questions)
FE (Field Engineer)
A network vendor sends out an FE to a down site.
Fedora Linux
Free and open source linux. New features are introduced here before migrating into Redhat Linux
FEX (Fabric Extender)
FIDO (Fast Identity Online)
E.g., “fido stick” for passwordless authentication.
FIFO (First in, First Out)
FIPS (Federal Information Processing Standard)
Government security practices. Best to avoid if possible.
FM (Fabric Manager)
I.e., the Gigamon Fabric Manager. A kind of informal acronym I just heard being used.
Fortran
A very basic procedural programming language once popular in the scientific and engineering communities.
Fuzzy Logic
Uses non-exact matching.
FMO (Future Mode of Operation)
As opposed to CMO.
FN (False Negative)
FO (Fiber Optic)
An informal abbreviation used by networking folks.
Forensics
Fortran
An ancient procedural programming language popular in the scientific and engineering communities from decades ago.
FOSS (Free and Open Source Software)
FP (False Positive)
FQDN (Fully Qualified Domain Name)
DNS term, e.g., support.paloaltonetworks.com as opposed to simply “support”
freeBSD
A Unix variant which still exists today.
Fritz!Box
A popular home router in Germany.
(Azure) Front Door
A scalable and secure entry point for fast delivery of global web applications.
FTE (Full Time Equivalent)
FW (Firewall)
GA (General Availability)
Gartner Group
A well-regarded research firm which reviews software and SaaS products. They decide which vendors are in the Magic Quadrant.
GBIC
A type of fiber optic transceiver that converts electric signals to optical signals.
GCP (Google Cloud Provider)
GDPR (General Data Protection Regulation)
An EU directive to achieve data privacy.
Generative AI
AI which can create new human-quality content, including text, images, audio or video.
Ghostscript
An open source postscript implementation.
GMP (Good Manufacturing Practice)
FDA lingo that implies their rules are being followed.
GMT – see UTC
gopher
An information retrieval protocol popular with libraries just prior to the web taking off.
GP (Global Protect)
Palo Alto Network’s name for their VPN offering.
GPT (Generative Pre-trained Transformer)
Perhaps the GPT in ChatGPT?
GPU (Graphical Processing Unit)
GPMI (General Purpose Media Interface)
The successor to HDMI in China.
GRC (Governance, Risk, and Compliance)
GRE
An encrypted tunneling protocol.
GRUB (probably stands for something silly because it’s linux after all)
Linux bootloader.
GSLB (Global Server Load Balancing)
Intelligent DNS-based load-balacing.
GSMO (Global Service Module Owner)
Not sure how widespread this usage is!
Guacamole
Or Apache Guacamole. An open source clientless remote desktop gateway often used in labs for training purposes
GUI (Graphical User Interface)
HA (High Availability)
Hallucination
When an LLM perceives patterns that are non-existent creating nonsensical or inaccurate outputs.
Hands and Eyes
When you don’t have physical access to a server, you need someone who does to be this for you.
HBM (High Bandwidth Memory)
HIBP (Have I Been Pwned)
HIP (Host Information Profile)
Only used in the world of Palo Alto Networks.
HLD (High Level Design)
HPC (High Performance Computing)
HSM (Hardware Security Module)
HSPA (High Speed Packet Access)
Telecom enhancements to 3G
HTML (HyperText Markup Language)
I started with version 0.9!
Hypervisor
IaaS (Infrastructure as a Service)
E.g., brining up a VM on AWS.
IAM (Identity and Access Management)
The governance, control, and monitoring of users’ identities and access within a system or network.
IANA (Internet Assigned Numbers Authority)
ICANN (Internet Corporation for Assigned Numbers and Names)
ICMP (Internet Control Messaging Protocol)
A sort of extra protocol for networks, not used for passing data, but information messages such as echo request and echo reply.
ICS (Industrial Control System)
IDE (Integrated Development Environment)
IDF (Intermediate Distribution Frame)
Distributes telecomm lines from an MDF to a workstation.
IdP (Identity Provider)
IDS (Intrusion Detection System)
IIS (Internet Information Server)
Microsoft’s web server.
ILEC (Incumbent Local Exchange Carrier)
IL
ILO (Integrated Lights Out Management)
A way to remotely control a server offered by HPE.
IMAP (Internet Message Access Protocol)
A slight improvement on POP3.
Incident Response Team
Variations include: Computer emergency Response team, Security incident Response Team, etc.
Infoblox
A DDI vendor whose products are considered best-in-class.
InTune
Used for enterprise software management, originally on smartphones, then extended to Windows and MAC OS.
IP (Internet Protocol)
IPv4 (Internet Protocol version 4)
IPv6 (Internet Protocol version 6)
IPAM (IP Address Management)
IPI (IP Intelligence)
At least in the world of F5 this means IP Intelligence, i.e., the reputation of a given IP address.
IPS (Intrusion Prevention System)
IPSEC
ISC (Internet Systems Consortium)
They develop and maintain Internet infrastructuire software such as BIND.
ISC2 (International Information System Security Certification Consortium)
Organization which specializes in training and certifications for cybersecurity professionals. Nothing at all to do with ISC despite the similar name!
ISO
Image file.
ITOM (IT Operations Management)
iRule
F5 specific lingo for programmable control over load-balancing and routing decisions. Uses the TCL language.
ISC (Internet Software Consortium)
A body which maintains an open source reference implementation for DNS (BIND) and DHCP.
ISO 9001
ISP (Internet Service Provider)
ITIL (IT Infrastructure Library)
IXP (Internet eXchange Point)
Probably more an informal acronym. Refers to a place where major carriers hand off Internet traffic. Like Ashburn, Virginia.
Java
A language which was going to change the world until it was ruined by Oracle.
JMRT (Juniper Malware Removal Tool)
JSON (JavaScript Object Notation)
Pronounced JAY-son. A popluar format for data exchange. Sort of human-friendly. Example: {“hi”:”there”,”subnets_ignore”:[“10/8″,”192.168/16”]}
Kanban
Agile way of tracking progress on tasks and brief meetings.
KB (Knowledge Base)
Informal but common abbreviation, e.g., Read the KB article before opening an incident.
Kernel mode
Kerning
Adjusting the spacing between letters in a proportional font.
KEV (Known Exploited vulnerabilities)
CISA maintains this catalog.
K8s (Kubernetes)
Open source system for automating deployment, scaling, and management of containerized applications
KQL (Kusto Query Language)
Used to query large datasets in Azure.
KVM (Kernel Virtual Module)
L2TP (Layer 2 Tunneling Protocol)
L3, L4, L7 (Layer 3, Layer 4, Layer 7)
Refers to OSI 7-layer traffic model. Layer 1: physical layer; Layer 2: Data Link Layer with MAC addresses; Layer 3: Network layer with protocols IP, ICMP and ARP; Layer 4: Transport layer with protocols TCP and UDP; Layer 5: session layer; Layer 6 presentation layer; Layer 7: application layer such as SMTP, HTTP, etc.
LACP (Link Aggregation Control Protocol)
Where you combine several physical interfaces into one logical port channel.
LAMP (Linux Apache MySQL and PHP)
An application stack which gives a server needed software to do “interesting things.”
LaTEX
A markup language based on TEX I used to use to write a scientific paper. I think it gets transformed into a DVI, and then into a postscript file.
LDAP (Lightweight Directory Access Protocol)
LEC (Local Exchange Carrier)
Link
Linux
Lisp
A programming language used by computer science types?
LiveSP
A Cisco enterprise metrics tool to provide visibility into LAN and WAN.
LLD (Low Level Design)
LLD (Low Level Discovery)
A command-line browser for unix systems.
LLDP (Link layer Discovery Protocol)
See also CDP
An open source OS similar to Unix.
LLM (Large Langiuage Model)
LTE (Long Term Evolution)
A type of wireless broadband used by telecoms.
lynx
A command-line browser for linux systems.
MAC (Media Access Control) Address
Layer 2 address of a device, e.g., fa-2f-36-b4-8c-f5
Machine Learning
A subfield of AI that deals with creating systems that can learn from data and improve their performance without explicit programming.
Magic Quadrant
Gartner’s trademarked term for vendors who exceed in both completeness of vision and ability to execute.
Management Plane
See Data Plane.
Mandiant
MD5 (Message Digest 5)
MDF (Main Distribution Frame)
Patch panels in a server room. They connect to IDFs.
MDM (Mobile Device Management)
Management software used to administer smartphones and tablets.
MELT (Metrics, Events, Logs, and Traces)
An acronym in the Observability space.
MFA (Multi Factor Authentication)
Mishing
An obscure security company probably trying to make a name for itself invented this one which will probably never catch on. Mobile-first phishing techniques: Smishing (SMS/text-based phishing), Quishing (QR code phishing), voice phishing, Wi-Fi-based phishing and more!
Modbus protocol
Modern Standby (MS)
Instant-on/instant-off type standby, but thde details are numerous. Read about it here: https://www.thewindowsclub.com/what-is-modern-standby
MPIP (Microsoft Purview Information Protection)
Has to do with information classification such as confidential versus public.
MS (Microsoft)
MS-CHAPv2
MS-MICE (Microsoft Miracast over Infrastructure Connection Establishment Protocol).
MS-NRTP (Microsoft .NET Remoting Traffic? Protocol)
But actually referred to as the .NET Remoting: Core Protocol Specification, which specifies a mechanism by which a calling program can invoke a method in a different address space over the network.
MSA (Modular Smart Array)
A SAN developed by HPE which features shared block-level storage.
MSI
A file type from Microsoft which is self-extracting and installs an application.
MSS (Maximum Segment Size)
Set by a TCP option in the beginning of the communcation.
MTTI (Mean Time To Identification)
Probably only Cisco uses this acronym e.g., in their ThousandEyes product.
MTTR (Mean Time To Resolution)
MTU (Maximum transmission unit)
Often 1500 bytes.
multicast
MVNO (Mobile Virtual Network Operator)
They buy network capacity frmo major US telecoms.
NAESAD (North American Energy Software Assurance Database)
Named pipes
I read it’s a Windows thing. huh. Hardly. It’s been on unix systems long before it was a twinkle in the eye of Bill gates. It acts like a pipe (|) except you give it a name in the filesystem and so it is a special file type. It’s used for inter-process communication.
NAT (Network Address Translation)
NDA (Non-Disclosure Agreement)
.NET
Netflow
Think of it like a call detail record for IP communications. Metadata for a communications stream.
Netscape
One of the original Internet-first companies. They built a pretty good browser which we used back in 1996. They also built web server and other server software and helped promulgate Java and javascript.
NFS (Network File System)
A file share protocol popular on Unix systems.
NGFW (Next Generation FireWall)
Palo Alto Networks describes their firewalls this way.
NGINX
A web server that is superioir to apache for most applications.
NIOS (Network Identity Operating System)
Core OS from Infoblox appliances.
NLP (Natural Language Processing)
A branch of AI that uses machine learning to enable computers to understand, interpret, and respond to human language.
NOC (Network Operations Center)
NNTP (Network News Transfer Protocl)
See Usenet.
North-South
Data movement from/to the data center. Also see East-West.
NQS (Network Queueing System)
We used to use NQS to distribute batch jobs amongst members of an Ultrix cluster.
NSA (National Security Agency)
NTLM
Relies on a three-way handshake between the client and server to authenticate a user.
NTU (Network Termination Unit)
Allows customer premises equipment to be connected to the switching equipment at the telco’s central office (CO)
Nvidia
World’s most advanced maker of chips used in AI.
OAuth bearer token
A security token with the property that any party in possession of the token (a “bearer“) can use the token in any way that any other party in possession of it can.
OCR (Optical Character Recognition)
OCSP
A service which tells you if a certificate has been revoked.
OIDC (OpenID Connect)
OKRs (Objectives and Key Results)
HR lingo.
OLAP (OnLine Analytical Processing)
Type of database which quickly responds to multi-dimensional queries.
OO (Object Oriented)
OOB (Out Of Band)
Example: the serial console of a security server.
OpenRoaming
openssl
A common open source implementation of SSL/TLS.
orca
A Microsoft editing tool – part of their SDK.
OS (Operating System)
OSFP (Open Shortest Path First)
OSI (Open Systems Interconnection)
OSS (Open Source Software)
OT (Operational Technology)
OTP (One-Time Password)
See also TOTP.
OV (Organization Validation)
A stronger form of SSL certificate validation than DCV. In OV CERTs, the CA verifies the legitimacy of the organization requesting the certificate. OV certificates display the organization’s name in the subject field.
ova
The image filetype for a virtual host.
Overlay
See underlay.
OWASP (Open Worldwide Application Security Project)
An online community that produces freely available articles, methodologies, documentation, tools, and technologies in the fields of IoT, system software and web application security.
P2V (Physical to Virtual)
Migrating a physical server to a VM.
PaaS (Platform as a Service)
PAM (Privilege Access Management)
PAN-OS
Palo Alto Networks name for its firewall OS.
PAP
Pascal
A simple programming language used to teach programming concepts.
Patch
PaaS (Platform as a Service)
PBF (Policy Based Forwarding)
PBR (Policy Based Routing)
PCI (Payment Card International?)
A standard which seeks to define security practices around the handling of credit cards.
PDF (Portable Document File)
PDU (Protocol Data Unit)
PE (Provider Edge)
Telecom lingo so cisco uses this term a lot.
PEM (Privacy Enhanced Mail)
The format certificates are normally stored in.
PHP (Probably stands for something)
A scripting language often used to program back-end web servers.
Photoshop
adobe’s photo-editing software. Considered the premier option.
PII (Personally Identifiable Information)
Ping
I guess we all know what it means. Usually implemented with ICMP.
PIP
Package management system for python.
pixel
PKCS (Public Key Cryptography Standard)
PKI (Public Key Infrastructure)
Plain Text
A human-readable format, i.e., no encyrption and not a binary file.
PLC (Programmable Logic Controller)
PM (Product Manager)
Could also be Project Manager but for me it usually means Product Manager.
PO (Purchase Order)
POC (Point of Contact)
POC (Proof of Concept)
PoP (Point of Presence)
An Internet provider has POPs in various locales.
POP3 (Post Office Protocol)
A very old protocol for mail servers and mail clients.
Port Channel
Portable Executable (PE)
POS (Point Of Sale)
I.e., what used to be called the cash register.
POTS (Plain Old Telephone Service)
Voice-grade telephone service employing analog signal transmission over copper
POV (Proof of Value)
PPT (PowerPoint)
A Powerpoint file.
Private Cloud
Prompt Engineering
The practice of crafting effective prompts that elicit high-quality answers from generative AI tools.
PS (PostScript)
A file type I used to use. It is a vector-oriented language, stack-based, which tells A printer how to move its ink pens around the page. Before there was PDF, there was postscript.
PS (PowerShell)
A versatile scripting language developed by Microsoft and available on all Windows computers.
PS (Professional Services)
Most IT vendors have a professional services line of business which would love to charge you extra to make their product actually work.
PSTN (Public Switched Telephone Network)
PTO (Paid Time Off)
Purple Team
Purple teams combine red team and blue team functions. See Red Team.
Putty
A popular software which implements an ssh client.
PXE (pronounced “pixie”)
A protocol offering a host a way to boot up via its network card.
PyPi (Python Package Index)
Python
A popular programming language, not the snake.
QR (Quick Response)
Those funny pixelated black-and-white sqaures which usuall;y convey a URL.
QSFP (Quad Small Form factor Pluggable)
A newer kind of SFP.
Quad9
A public DNS resolver with IP 9.9.9.9 run by a Swiss non-profit.
Quishing
QR-code phishing.
R
A development language popular in the data science community.
RACI (Responsible, Accountable, Consulted, Informed)
Project managers love this.
Rack Unit
RADIUS
RAE (Remote Apple Events)
RAG (Retrieval Augmented Generation)
A method to customize LLMs by allowing it to train on internal data sources.
Ray
An open-source unified compute framework used by the likes of OpenAI, Uber, and Amazon which simplifies the scaling of AI and Python workloads, including everything from reinforcement learning and deep learning to tuning and model serving.
RBAC (Role-Based Access Control)
RDAP (Registry Data Access Protocol)
Related to a domain’s whois information. See RFC 7482.
RDP (Remote Desktop Protocol)
Real Time
A real time OS is one which guarantees execution of the highest priority process.
Recursive
A function which calls itself.
Redhat Linux
A commercialized version of Fedora whose packages are always dated, usually by years.
Redirect
Relational Database
The traditional database with tables of rows of columns.
Remediation
Addressing a security flaw.
Remote Desktop Licensing (RDL) services
Often deployed on Windows severs with Remote Desktop Services deployed.
Responsive Design
Really, it just means an app alters its appearance to fit the device from which it is being used.
Retrieval-Augmented Generation (RAG)
Adding internal documents to your language model.
Reverse Engineer
To figure out the basic building blocks or code by first observing behavior of a system.
Reverse Proxy
A TCP gateway which terminates a tcp connection and maintains a separate tcp connection to a back-end server.
RFC (Request for Comment)
RFI (Requst for Information)
RFO (Reason for Outage)
RFP (Request for Proposal)
RFQ (Request for Quote)
RHSA (Redhat Security Advisory)
RIB (Routing Information base)
The route table as seen by a router, including AS paths.
RIPE
RIR (Regional Internet Registry)
The place where ASN <-> IP prefix pairs are registered. The RIRs are ARIN, RIPE, APNIC, LACNIC and AFRINIC.
RISC (Reduced Instruction Set Architecture)
A family of CPUs. As opposed to CISC.
RLHF (Reinforcement Learning from Human Feedback)
Where humans review output of LLM’s to help refine them.
RMA (Return Merchandise Authorization)
You hear this a lot when It guys need to get a replacement for failed equipment.
RMM (Remote Monitoring and Management)
A software platform that allows IT service providers to monitor and manage their clients’ IT systems remotely.
ROA (Route Origin Authorization)
ROCE (Return on Capital Employed)
Hey, an IT person has to know a few business terms!
Round Robin
A load balancing algorithm where each back-end server is used in a rotating sequence.
Route 53
In AWS-land, an intellugent DNS service, i.e., geoDNS +.
RPC (Remote Procedure Call)
RPKI (Resource Public key Infrastructure)
Provides a way to connect Internet number resource information to a trust anchor.
RPi (Raspberry Pi)
A popular small, inexpensive server aimed at the educational crowd.
RPM (Redhat Package Manager)
RPZ (Response Policy Zone)
A concept in DNS for either a DNS firewall or way to overwrite DNS responses.
RR (Resource Record)
RSA
Asymmetric encryption standard named after its creators, Ron Rivest, Adi Shamir and Leonard Adleman.
RSRP (Reference Signal Received Power)
Mobile network term.
RSRQ (Reference Signal Received Quality)
Mobile network term.
RSSI (Received Signal Strength Indicator)
It’s a mobile network term.
RTFM (Read The “flippin” Manual)
RTT (Round Trip Time)
s3
blob storage service in AWS
SaaS (Software as a Service)
SAMBA (SMB something or other)
Open source SMB implementation offered on Linux.
SAML (Security Association Markup language)
SAN (Storage Area Network)
SAN (Subject Alternative Name)
In certificate-land, an extension field which lists all the various names for which this certificate is authorized for.
SANS
Private outfit in the US which specializes in information security and cybersecurity training.
Sans-Serif
A font type which does not have the fancy rounded blobs at the tips of the letter, such as Helvetica.
SAP
The largest software company no one knows about because they sell hugely overpriced ERP systems to the few companies which can afford it.
SAS (Shared Access Signature)
Azure-specific term. Provides access rights to blobs, files, etc.
SASE (Secure Access Service Edge)
Palo Alto Networks likes to think they invented this term, but once Gartner started to use it they went on to embrace some other term. Or maybe it was the other way around.
SCADA (Supervisory Control and Data Acquisition)
That’s for OT stuff.
Scale sets
In cloud, a service which automates the build-up or tear-down of VMs behind a load balancer.
SCCM (System Center Configuration Manager)
Microsoft’s older enterprise software management offering.
scp (Secure CP)
A network-aware version of the linux cp command whose transport is ssh.
SDK (Software Development Kit)
SDWAN (Software defined WAN)
SE (Sales Engineer)
Sentinel
I need to learn this myself. It just came up today.
SEO (Search Engine Optimization)
SFP (Small Form factor Pluggable)
A type of optic transceiver that converts electric signals to optical signals.
SGML (Standard Generalized Markup Language)
If you ask the French they proudly point to this as the predeccesor, invented in France, of course, to the more widely known HTML.
SFTP (Secure file Transfer Protocol)
SHA (Secure Hash Algorithm)
Shadow IT
IT spend that’s under the radar of corporate.
Signature
A matchable pattern in analyzed data, .e.g., the checksum for an executable.
SIEM (Security Information and Event Management)
SINR (Signal to Interference and Noise Ratio)
Mobile network term. See also RSRP, etc.
SIP (Session Initiation Protocol)
Used in voice over IP.
SLAAC (Stateless Address Autoconfiguration)
In ipv6-land devices can generate their own addresses by combining network prefixes with their interface identifiers.
SMB
Old protocol used for Windows file shares.
SLS (Strata Logging Service)
It’s a Palo Alto Networks thing.
SME (Subject Matter Expert)
S/MIME (Secure/Multipurpose Internet Mail Extensions)
A standard for public key encryption and digital signatures that is used to secure email communications
SMP (Symmetric Multi Processing)
SMTP (Secure Mail Transfer Protocol)
SNAT (Source NAT)
SNI (Server Name Indication or similar, I think)
When multiple HTTPS web sites share a single IP this technology can be used to identify which certificate to send to a requester.
SNMP (Simple Network Management Protocol)
All security appliances support this protocol which permits system monitoring.
SNORT (probably is an awkward acronym)
An open source rule-matching engine to scan network traffic and serve as an IDS.
SOC (System on a Chip)
I believe the RPi is described to be this.
SOC (Security Operations Center)
Solaris
A Unix variant possibly still available. Offered by Oracle and formerly Sun Microsystems Corporation. Was cool and innovative in its day.
SPN (Security Processing Node)
Palo Alto Networks lingo for a cloud firewall which terminates IPSEC connections from a Remote Network (also their lingo).
SPOC (Special Point Of Contact)
Probably only used at companies where I have worked, but just for the record… It’s funny when you hear someone referred to as a “Spock.”
Spoofing
When a source IP address is faked.
SQL
SR (Short Range)
An informal abbreviation used by networking folks.
SRE (Site Reliability Engineer)
SSE (Security Service Edge)
Gartner loves this term.
SSH (Secuire Shell)
SSL (Secure Socket Layer)
SSL Labs
A Qualys (so you know it has to be good quality) service where you can test a web site’s SSL certificate.
SSO (Single Sign On)
Steal with Pride
To unashamedly build on someone else’s work.
Sticky Session
In a load-balanced environment, the ability to direct client traffic from a unique client to the same back-end server.
STUN
Protocol somehow related to DTLS and maybe also SIP.
SunOS
Before Solaris there was SunOS, a BSD flavor of Unix, I believe, offered by Sun.
SVI (Switch virtual Interface)
A layer 3 on-switch routing between vlans on that switch. It’s a Cisco thing.
TAC (Technical Account or something?)
TAM (Technical Account Manager)
Another Cisco term.
Cisco uses this term a lot.
TCP (Transport Control Protocol)
TCS (Tata Consultancy Services)
Indian outsourcer.
TeamViewer
A remote management tool.
Telegram
A secure and private messaging platform.
Telnet
Terraform
Tool which simplifies cloud deployments.
The epoch
The first moment of January 1st, 1970
TI (Threat Intelligence)
Time Series
A way to represent data which comes in streams over time.
TLP (Traffic Light Protocol)
TLS (Transport Layer Security)
Tooltip
An element of a graphical user interface in the form of a box of text that appears when a cursor is made to hover over an item; normally used to explain the function of the item.
TOPS 20
A timeshare operating system from DEC which I used in college.
TOTP (Time-based One-Time Password)
TPM (Trusted Platform Module)
TPM, a Microsoft security feature required by Windows 11, is a dedicated chip designed to provide “hardware-level security services for your device,” keeping your private information and credentials safe from unauthorized users.
TPU
My favorite editor in the VAX/VMS world. Successor of EDT.
TS (TroubleShooting)
Informal abbreviation.
TSA (Transitional Service Agreement)
May not be in widespread use.
TSF (Tech Support File)
Palo Alto Networks-specific lingo for a dump file they require for a firewall support case.
TSID (Threat Signature Indicator)
Only used in the world of Palo Alto Networks.
TW (Time Window)
Ubuntu Linux
A commercialized implementation of Debian Linux from Canonical.
UC (Unified Communications)
Cisco likes this term.
UC (Use Case)
udev rules
udev rules in Linux are used to manage device nodes in the /dev directory. Those nodes are created and removed every time a user connects or disconnects a device.
UFS (Unmanaged File Service)
Term probably specific to a company where I worked, but oh well, that’s how acronyms get started.
UEFI (Unified Extensible Firmware Interface)
It’s like the boot environment, used by Windows OSes.
UI5
SAP’s UI for HTML 5.
Ultrix
A legacy Unix variant which ran on DEC workstations in the 90’s.
Underlay
SD Wan terminology for the underlying network. As opposed to overlay.
Unit testing
UPS (Uninterruptible Power Supply)
URL
USB (Universal Serial Bus)
Usenet
In the old pre-reddit days, these were forums to discuss specific topics which had its own protocol, NNTP.
UTC (Universal Time Coordinated)
What used to be called GMT.
UTF-8
Common representation of common language characters. I think of it as a successor to ASCII.
Validated
In FDA parlance, an adjective used to describe a system which follows FDA controls. It’s usually a pain in the rear to run a validated system, e.g., as part of a GMP environment.
VAX (probably stands for something)
A legacy line of micro-computers sold by Digital Equipment Corporation, as in, the VAX 8600. The OS was called VMS.
VAX/VMS
See entry for VAX.
VDI
A virtual desktop offered by Citrix.
Veriexec (Verified Exec)
A Juniper device kernel-based file integrity subsystem that protects the OS from unauthorized code binaries
VCU (Video Conference Unit)
Cisco terminology.
VLAN
VM (Virtual Machine)
VM/CMS
A piece of crap operating system for IBM mainframes back in the day. As I recall essentially everything had to be submitted as a batch job.
VMSS (Virtual machine Scale Set)
Azure uses this abbreviation.
VMWare
Will Broadcom destroy this company the way they did to Bluecoat/Symantec?
VNC (Virtual Networking Computer)
VNC is a software used to remotely control a computer.
Vnet (Virtual Network)
Isolated network within a larger network in a cloud environment.
VOIP (Voice Over IP)
As opposed to analog phone lines.
VPC (Virtual Private Cloud)
vPC (Virtual Port Channel)
A virtual port channel (vPC) allows links that are physically connected to two different Cisco FEXes to appear as a single port channel by a third device.
VPG (Virtual Port Group)
A Cisco-ism.
VPN – Virtual Private Network
VRF
A logically separated network when using MPLS.
vsys
In PaloAlto Networks terminology, a virtual partition of a physical firewall so that multiple vsys can be on one physical box.
WAIS (Wide Area Information System, or something like that)
Another competitor to the world wide web. I believe Brewster Kahle was behind it?
WAP (Wireless Access Point)
WARP (Web Application Response Protocol)
Designed to improve the performance of web applications by optimizing the way data is transmitted over the internet.
Waterfall
A discredited approach to software development.
WEBDAV (Web Distributed Authoring and Versioning)
Webhook
Website
Whois
Old-timey service which gives you registrar info about a DNS domain. These days most everything is blocked for privacy reasons.
Wiki
A less formal and usually more collaborative approach to documentation, the prime example being Wikipedia.
Windows PE or Win PE
A small OS for repairing or restoring Windows systems.
WLC (Wireless LAN Controller)
WSUS (Windows Server Update Services)
Enables administrators to manage the distribution of updates and hotfixes for Windows servers in an enterprise.
WWW (World Wide Web)
X
Formerly knownm as Twitter. Elon Musk’s disastrous attempt at social media.
x86
A type of processor architecture. Found in most Windows PCs.
XHR (XMLHttpRequest)
I.e., ajax.
XML (eXtensible Markup Language)
Common file format for data exchange, but not too human-friendly.
x-mosaic
This is the browser I used in 1993. It was the Mosaic browser for X-Windows, developed by none other than Marc Andreesson.
X-Windows
The GUI environment for Unix. Most of its utilities have names beginning with x such as xterm.
YAML
YARA
Zabbix
An open source infrastructure monitoring system.
XML (eXtensible Markup Language)
Markup language and file format for storing, transmitting, and reconstructing data. It defines a set of rules for encoding documents in a format that is both human-readable and machine-readable.
ZTNA (Zero Trust Network Architecture)
Assumes tha even on your Intranet you can’t trust anyone trying to access your systems until they’ve been vetted, each and every time.